Detect and respond to high-risk threats in your logs with Google Cloud
Editor's Note: This the fourth blog and video in our six-part series on how to use Cloud Security Command Center. There are links to the three previous blogs and videos at the end of this post.
Data breaches aren’t only getting more frequent, they’re getting more expensive. With regulatory and compliance fines, and business resources being allocated to remediation, the costs from a data breach can quickly add up. In fact, the average total cost of a data breach in the U.S. has risen to $3.92 million, 1.5% more expensive than in 2018, and 12% more expensive than five years ago, according to IBM.
Today, we’re going to look at how Event Threat Detection can notify you of high-risk and costly threats in your logs and help you respond. Here’s a video—that’s also embedded at the end of this post—that will help you learn more about how it works.
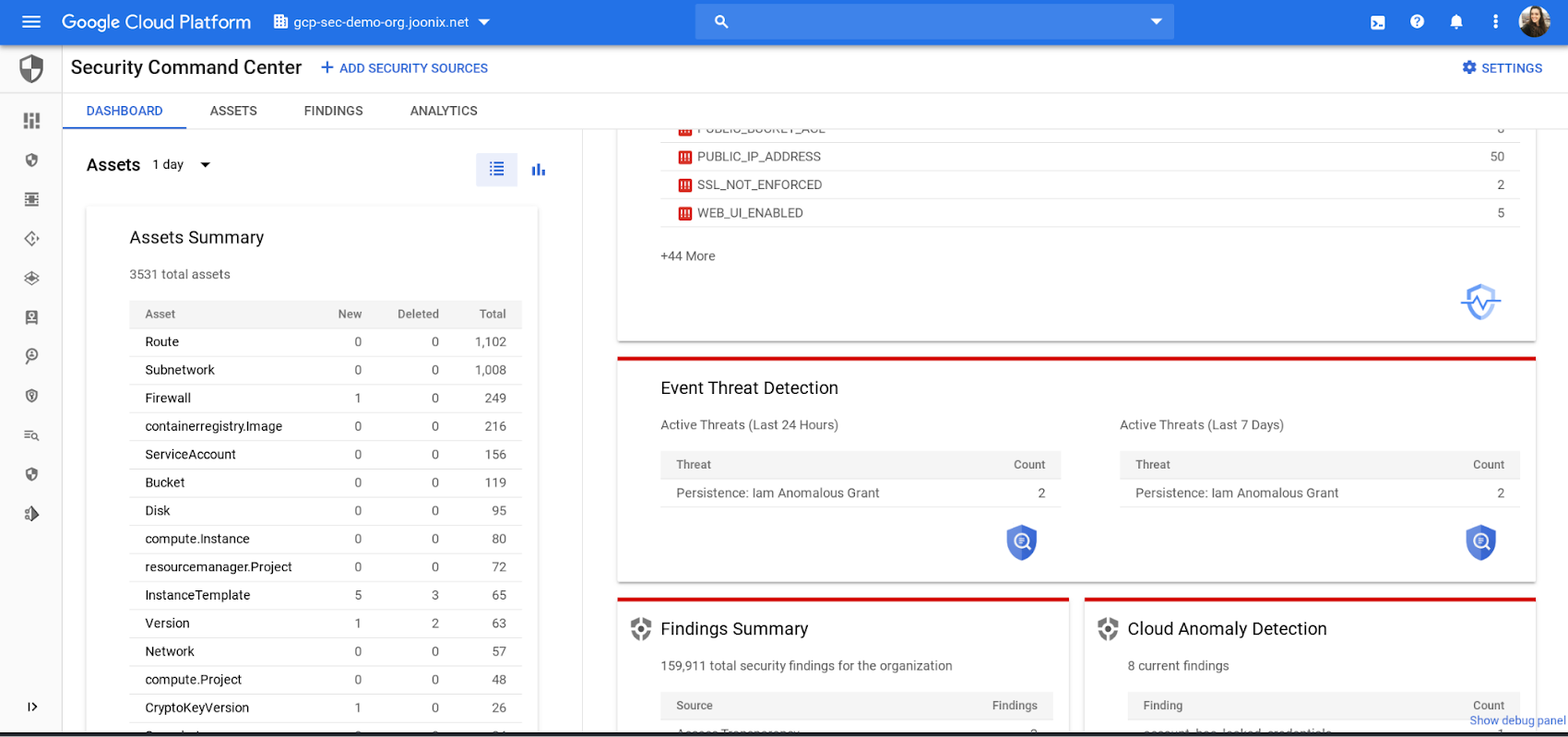
Enabling Event Threat DetectionOnce you’re onboard, Event Threat Detection will appear as a card on the Cloud Security Command Center (Cloud SCC) dashboard.
Event Threat Detection works by consuming Cloud Audit, VPC flow, Cloud DNS, and Syslog via fluentd logs and analyzing them with our threat detection logic and Google’s threat intelligence. When it detects a threat, Event Threat Detection writes findings (results) to Cloud SCC and to a logging project. For this blog and video, we’ll focus on the Event Threat Detection findings available in Cloud SCC.
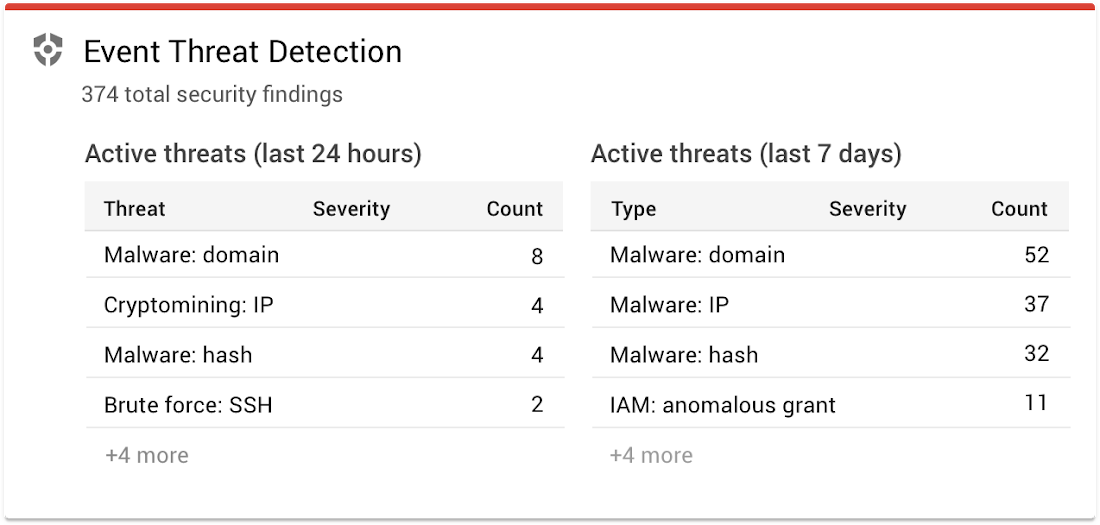
Detecting threats with Event Threat DetectionHere are the threats Event Threat Detection can detect in your logs, and how they work:
- Brute force SSH: Event Threat Detection detects the brute force of SSH by examining Linux Auth logs for repeated failures followed by success.
- Cryptomining: Event Threat Detection detects coin mining malware by examining VPC logs for connections to known bad domains for mining pools and other log data.
- Cloud IAM abuse Malicious grants: Event Threat Detection detects the addition of accounts from outside of your organization’s domain that are given Owner or Editor permission at the organization or project level.
- Malware: Event Threat Detection detects Malware in a similar fashion to crypto mining, as it examines VPC logs for connections to known bad domains and other log data.
- Phishing: Event Threat Detection detects Phishing by examining VPC logs for connections and other log data.
- Outgoing DDoS, port-scanning: Event Threat Detection detects DDoS attacks originating inside your organization by looking at the sizes, types, and numbers of VPC flow logs. Outgoing DDoS is a common use of compromised instances and projects by attackers. Port scanning is a common indication of an attacker getting ready for lateral movement in a project.
Responding to threats with Event Threat DetectionWhen a threat is detected, you can see when it happened—either in the last 24 hours or last 7 days—and how many times it was detected, via the count.
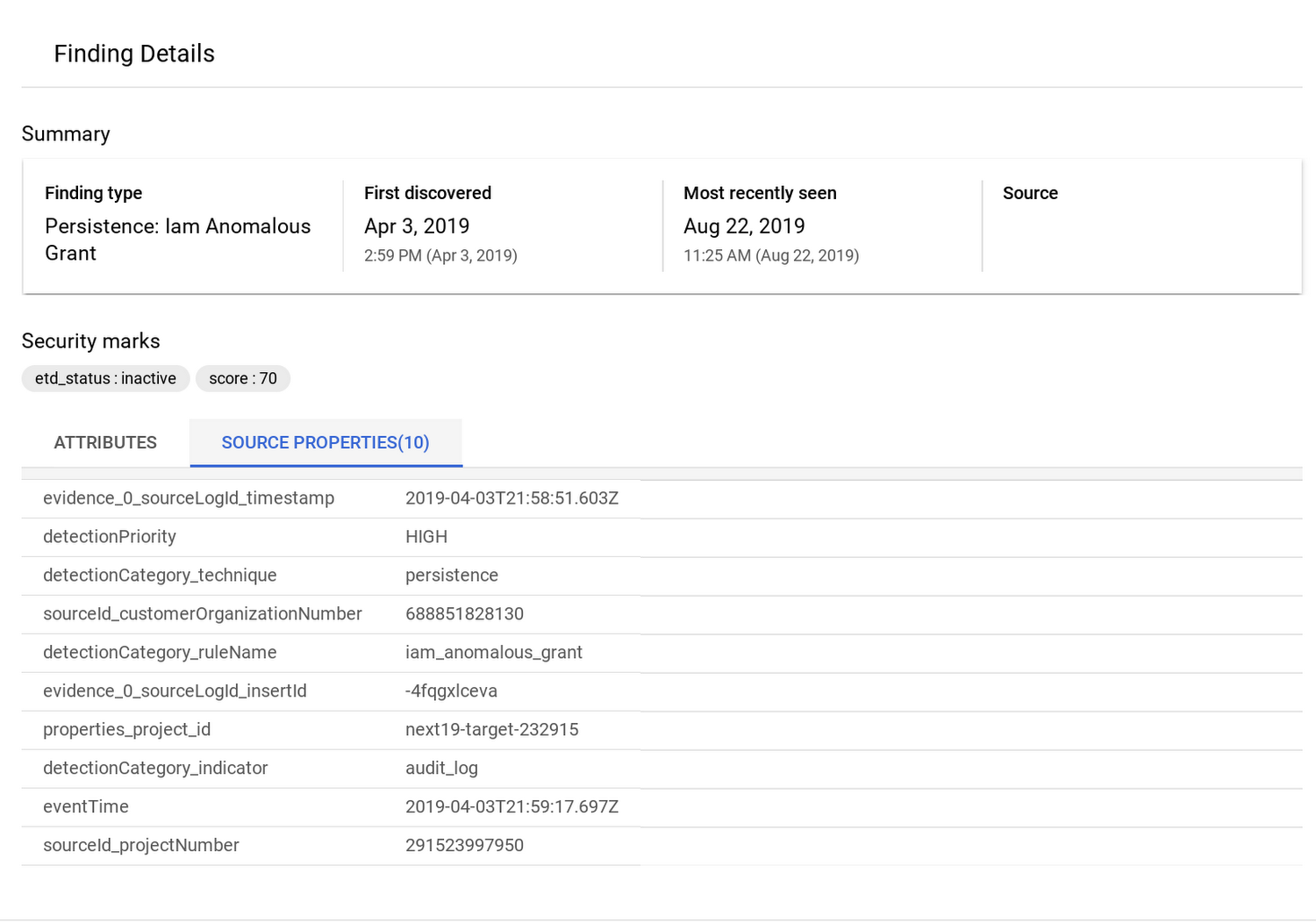
When you click on a finding, you can see what the event was, when it occurred, and what source the data came from. This information saves time and lets you focus on remediation.
To further investigate a threat detected by Event Threat Detection, you can send your logs to a SIEM. Because Event Threat Detection has already processed your logs, you can send only high value incidents to your SIEM, saving time and money.
You can use a Splunk connector to export these logs. Splunk automatically sorts your key issues—you can see events and categories—so you can investigate further and follow the prescribed steps.
To learn more about how Event Threat Detection can help you can detect threats in your logs, watch our video.


Comments
Post a Comment