Safety first: Announcing 11 new G Suite security features
With so many people working remotely, it's more important than ever that the tools we use to stay in touch and productive are safe and secure. That’s why today we’re announcing new updates that provide even stronger security in Gmail, Meet, and Chat. We’re also unveiling new ways to help IT admins easily manage and secure devices in the Admin Console.
Support for the BIMI standard in Gmail
While we have many defenses built into Gmail, we recognize that email functions in a large, complex, interconnected ecosystem. This is why we’re working not just to keep Gmail safe, but to help keep the entire ecosystem secure.
We do this in many ways: by making our technology available to others, as we’ve done with Safe Browsing and TensorFlow Extended (TFX); by collaborating and sharing best practices in industry working groups; and by helping create and shape many of the standards that secure email today.
Today, we’re excited to announce the pilot of another standard we’ve been working on: Brand Indicators for Message Identification (BIMI). Our BIMI pilot will enable organizations, who authenticate their emails using DMARC, to validate ownership of their corporate logos and securely transmit them to Google. Once these authenticated emails pass all of our other anti-abuse checks, Gmail will start displaying the logo in existing avatar slots in the Gmail UI.
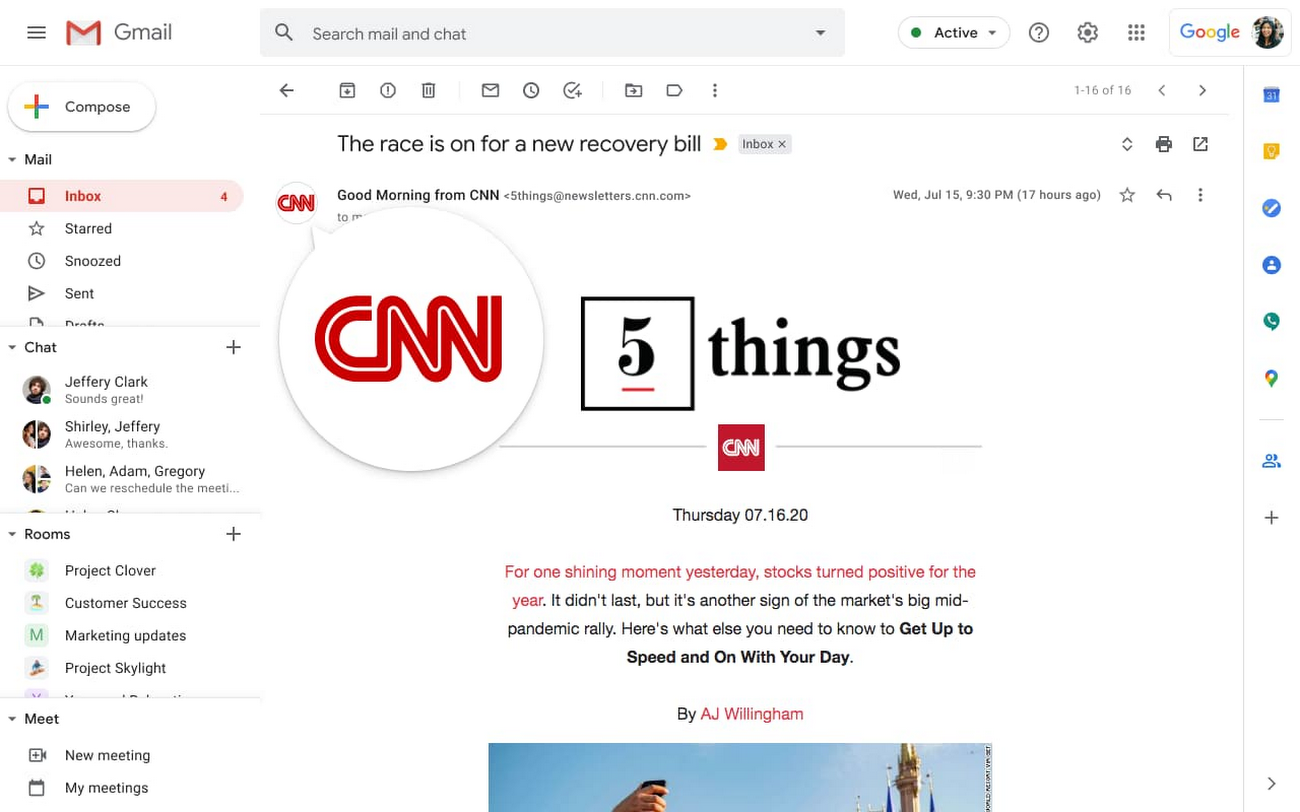
BIMI provides benefits to the whole email ecosystem. By requiring strong authentication, users and email security systems can have increased confidence in the source of emails, and senders will be able to leverage their brand trust and provide their customers with a more immersive experience.
“For organizations that want to create a trusted brand presence over email, BIMI is a great opportunity, incentivizing them to implement strong authentication, which in turn will lead to a safer, more trusted email ecosystem for everyone,” said Seth Blank, Chair of the AuthIndicators Working Group, and Vice President, Standards and Technologies, Valimail
We’ll be starting the BIMI pilot in the coming weeks with a limited number of senders, and with two Certification Authorities to validate logo ownership: Entrust Datacard and DigiCert. To prepare for the post-pilot launch of BIMI and to generally help secure the ecosystem, we encourage organizations to start adopting DMARC. We look forward to a successful pilot, and to making BIMI generally available in the coming months, at which point organizations can choose if they want to adopt this standard. To learn more about BIMI, visit the working group’s website.
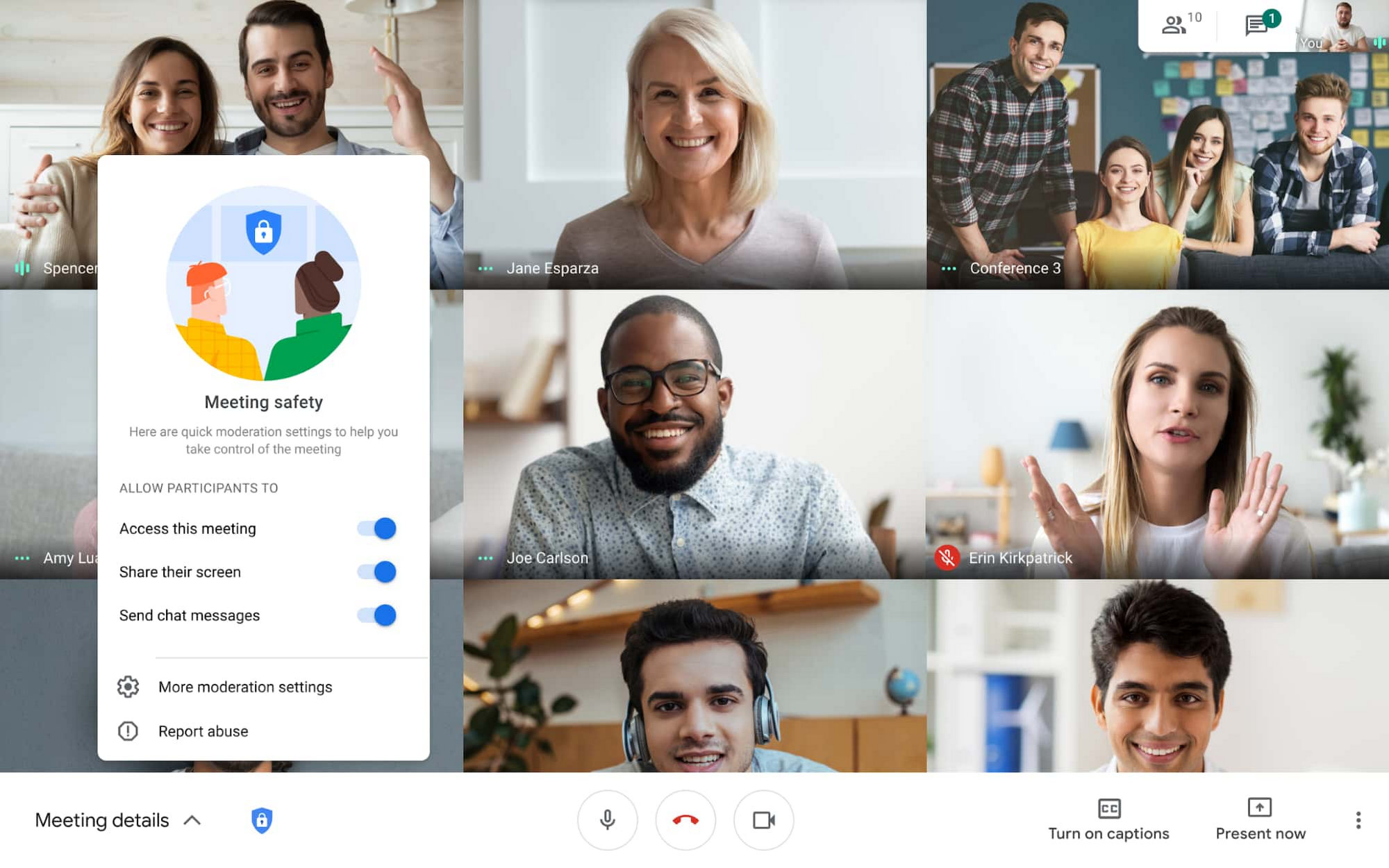
New controls for Meet
Like Gmail, Google Meet securely connects people around the world. With people relying on Meet now more than ever, we're working hard on new ways to keep video collaboration secure. In the coming weeks, we’ll be rolling out new security controls to help ensure that only intended participants are let into a video meeting. In the initial rollout, these options will be available for consumer and G Suite for Education accounts.
First, we’re giving meeting hosts increased control over who can “knock” and join their meetings. Enhanced meeting knocking builds on existing controls that require those not included on a meeting’s calendar invite to explicitly knock and ask to be admitted to a meeting.
Once an attendee is ejected, they won't be able to attempt to join the same meeting again by knocking, unless the host re-invites them.
If a knocking request from a user has been denied multiple times, the user will be automatically blocked from sending more requests to join the meeting.
Second, we’re giving hosts advanced safety locks so they can better protect meetings with a few simple clicks.
With the safety locks, hosts can decide which methods of joining (via calendar invite or phone, for example) require users to obtain explicit approval to join.
Engaging safety locks will block all anonymous users’ (users not logged into a Google account) attempts to join a meeting, and enforce the requirement that the host joins first, for example.
Specific safety locks enable the host to control the level of participant interactivity in the meeting. The chat lock and present lock will let hosts control which attendees can chat and present within the meeting.
New security features in Chat
Chat helps teams stay efficient, productive, and collaborative, whether they’re working from home, the office, or anywhere else. We’re rolling out new security features to make your Chat conversations even safer:
We are extending the strong phishing protections we have built within Gmail to Chat. If a link is sent to you via Chat, it will be checked against real-time data from Safe Browsing and flagged if it’s found to be malicious.
In the coming weeks, you’ll be able to report and block Chat Rooms if you suspect malicious activity in one.
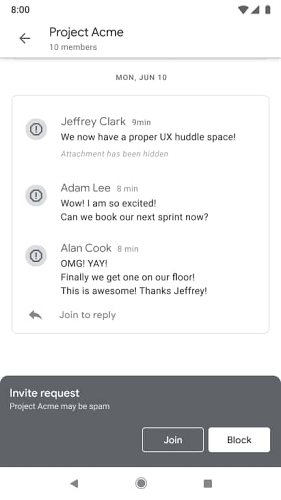
By taking advantage of security signals in Chat, as well as the rest of G Suite, we automatically detect and limit abusive content. For instance, spammy invitations can be classified as spam and in some cases automatically blocked.
Easier management and additional security controls for admins
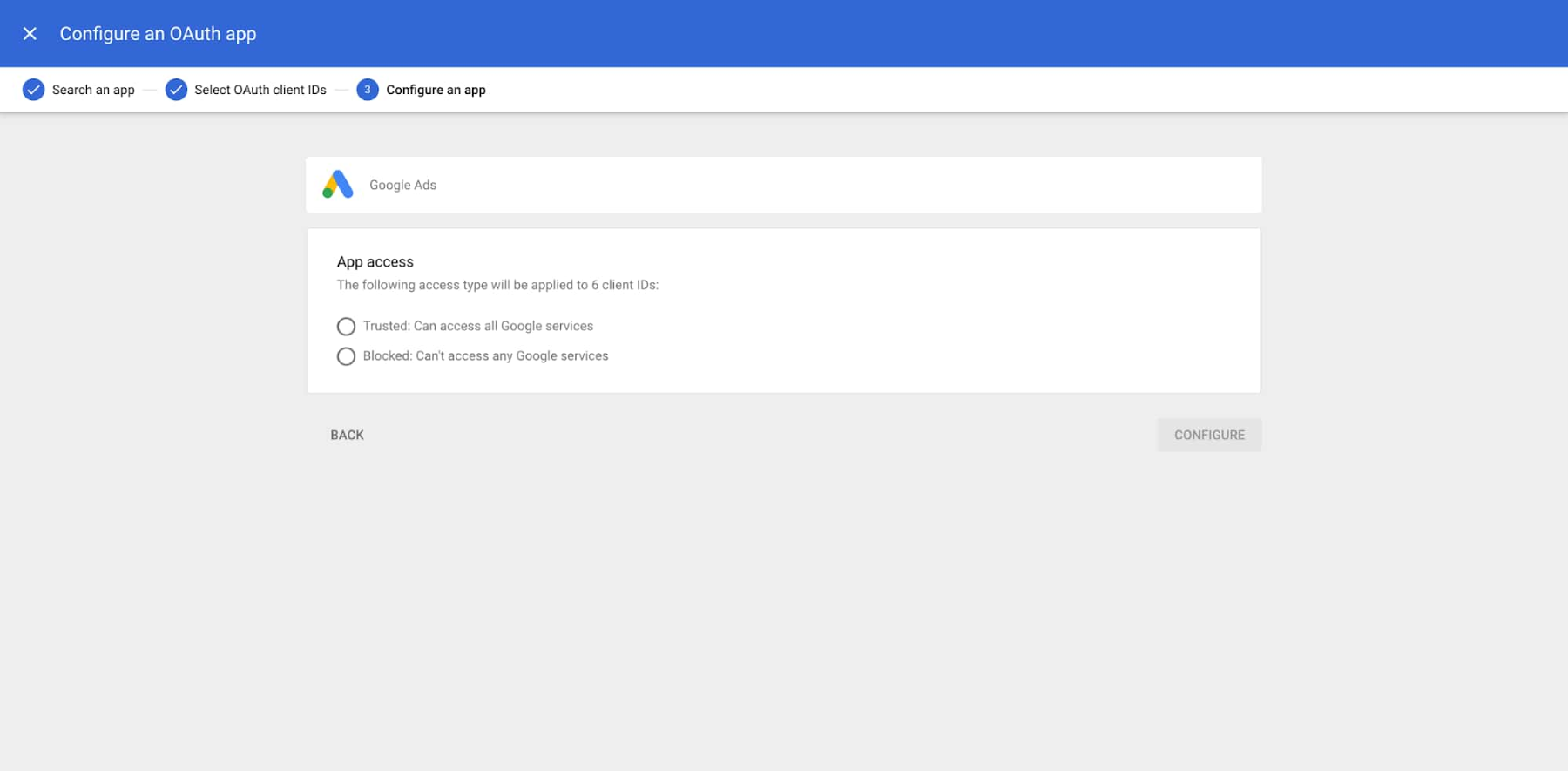
The way we work looks very different now than it did six months ago, and IT admins are at the center of keeping their workforces online, productive, and secure. We’re introducing several new features to help admins keep their organizations secure. First, we’re simplifying and enhancing device management.
We've redesigned the devices page in the G Suite admin console to include more intuitive navigation for device management and to quickly display the number of devices managed by each service.
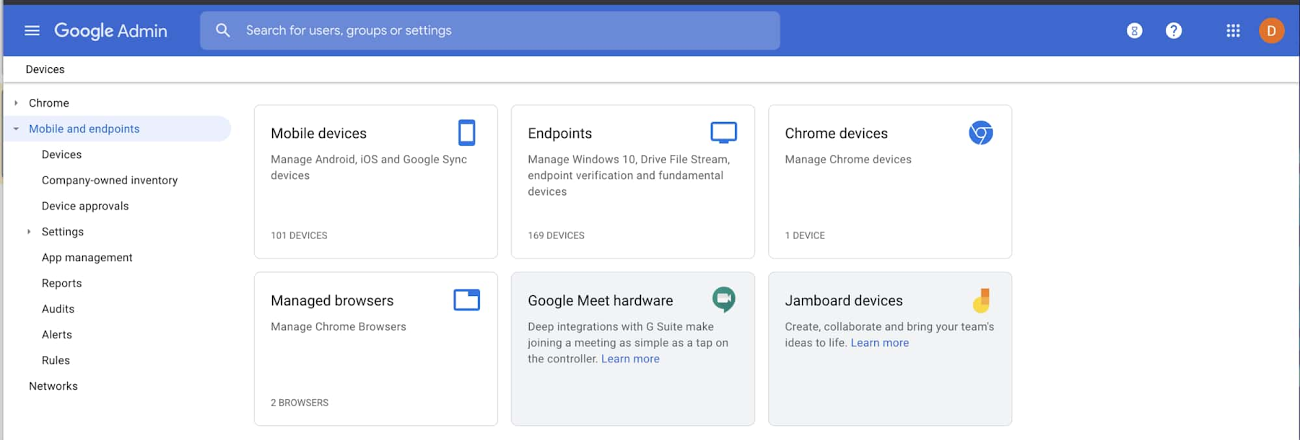
We’re also launching our integration with Apple Business Manager (formerly DEP) to provide G Suite Enterprise, G Suite Enterprise Essentials, Cloud Identity Premium, and G Suite Enterprise for Education admins the ability to simply and securely distribute and manage company-owned Apple iOS devices.
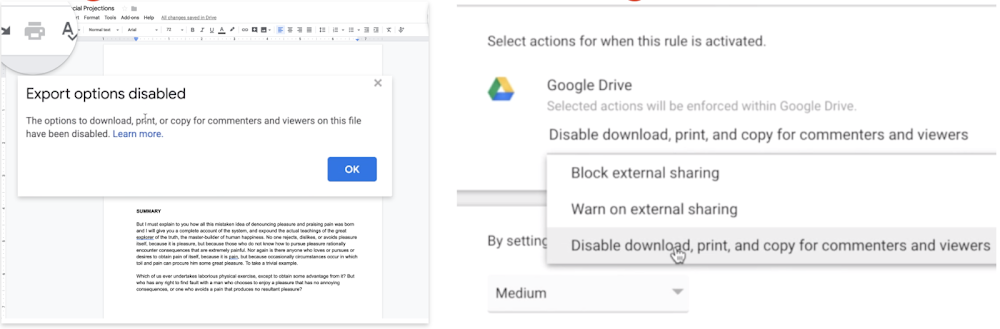
Second, we’ve always prioritized keeping your sensitive data protected and private, and today we’re announcing another enhancement to our Data Loss Prevention feature that helps prevent unauthorized access to data.
Admins can now use automated information rights management (IRM) controls to prevent data exfiltration by blocking end users from downloading, printing, or copying Google Drive docs, sheets, and slides that contain sensitive content.
These controls tie in with the Data Loss Prevention rules that have been set for the organization, and admins can run a full scan of all files within Google Drive and automatically enable these controls for all users.
These features are now available in Beta to G Suite Enterprise, G Suite Enterprise Essentials, and G Suite Enterprise for Education customers.


Excellent post. I really enjoy reading and also appreciate your work. This concept is a good way to enhance knowledge. Keep sharing this kind of articles, Safety First Training Ltd. Thank you.
ReplyDeleteI am pleased that this post provided me with some important information. After reading it, I feel you have exceptional knowledge. Thank you for providing information about online safety courses. Keep up the excellent job.
ReplyDeleteExcellent post. I really enjoy reading and also appreciate your work. This concept is a good way to enhance knowledge. Keep sharing this kind of articles, security guarding course ealing uk Thank you.
ReplyDeleteA very delightful article that you have shared here. Your blog is a valuable and engaging article for us, and also I will share it with my companions who need this info, Counter Security Services Ltd Thankful to you for sharing an article like this.
ReplyDeleteHey friend, it is very well written article, thank you for the valuable and useful information you provide in this post. Keep up the good work! FYI, >physics wallah neet modules pdf free download,10 Lines on Rose in English, Ghost stories from the Indian Hills by Ruskin Bond Book Review
ReplyDeleteHey friend, it is very well written article, thank you for the valuable and useful information you provide in this post. Keep up the good work! FYI, Chase Sapphire Reserve credit card review, physics wallah neet modules pdf free download,10 Lines on Rose in English, Ghost stories from the Indian Hills by Ruskin Bond Book Review
ReplyDelete