Security-at-scale: 10 new security and management controls
With so many people working remotely, it's imperative that the tools we use to stay productive are secure. Already this year we have worked to strengthen security for our customers and help make threat defense more effective.
Today, we’re sharing new advancements that provide robust controls, enable automation, and simplify managing security-at-scale with both G Suite and Google Cloud Platform.
Enabling extensibility through APIs
First, let’s take a look at enabling extensibility with APIs with the general availability of both Cloud Identity groups API and service account API access for Cloud Identity customers. We recognize that some Google Cloud customers rely heavily on groups but are not G Suite administrators. We are now enabling programmatic access to manage groups without requiring admin roles with Cloud Identity groups API. With this feature, we’ve expanded access to non-admin service accounts and users as group owners and managers.Further, you can programmatically manage groups using service accounts without needing to grant domain-wide delegation or use admin impersonation with service account API access. Hand-in-hand with this feature is service accounts as members, in general availability, which natively supports service accounts in groups without changing group settings, and indicates if a member is a service account. These features also allow for more accurate visibility into actions taken by service accounts; now, audit logs will show the service account as the actor as opposed to an impersonated user via domain-wide delegation.
“Before API access without domain wide delegation, we required many Group Admin accounts to manage the capability. We are now able to limit access to only those who absolutely need it, helping us to strengthen our security posture.” - Woolworths
Next, we’re adding to G Suite’s Vault API with the general availability of Count API. This API enables you to see the number of messages, files, or other data items that match a search query. Since this functionality can help you estimate the size of an export, Count API helps you ensure a successful export by reducing the likelihood of export errors due to size.
Saving time and effort with group membership automation
We’re helping Cloud Identity customers save time and effort with new automation in group membership. Complete automation of group membership is possible with dynamic groups, now in beta. By simply utilizing the appropriate user attributes in a membership query, you can create groups whose membership is automatically kept up-to-date.
We’re also introducing membership expiration for Cloud Identity in beta, which allows you to set a time-based expiration on group membership to automatically revoke group membership once the specified time period has passed. This can be especially useful to allow engineers to debug in production for a limited time, or grant temporary contractors or vendors time-based access to resources, for example.
Adding controls to enhance security
We want our customers to feel empowered with all of the controls they need to customize security according to their organization’s needs. Here are some ways that we’re giving you even greater control to meet your security objectives when managing groups.With security groups for Cloud Identity, now in beta, you can add security labels to groups to differentiate between groups used for access control and those only used for email or other communication. This labeling helps you ensure that security groups cannot contain any groups from outside of your organization or email-only groups.
Next, to give you more control in managing groups, we launched the beta of groups in GCP console in May. With this feature, we’ve simplified creating groups, adding users, and assigning permission. You can try it here.
Use visibility and insights to strategically prioritize your security efforts
Having visibility into the access and data within your organization is a critical step in protecting it. Taking that a step further, having insights to act upon helps you strategically prioritize your security efforts.
First, let’s talk about the visibility you’ll gain with indirect membership visibility & hierarchy APIs, now in beta for Cloud Identity. To help you easily visualize group membership, this feature allows you to view all direct and indirect members of a group, view all direct and indirect memberships of a user, and find paths from a user to a group. In addition, with a new check API, you can identify if an account is a member of a given group or not. You’ll get all of the information you need to create visualization of complex group structures and hierarchies. Having this kind of membership visibility can help you make decisions about who to add to or remove from your groups.
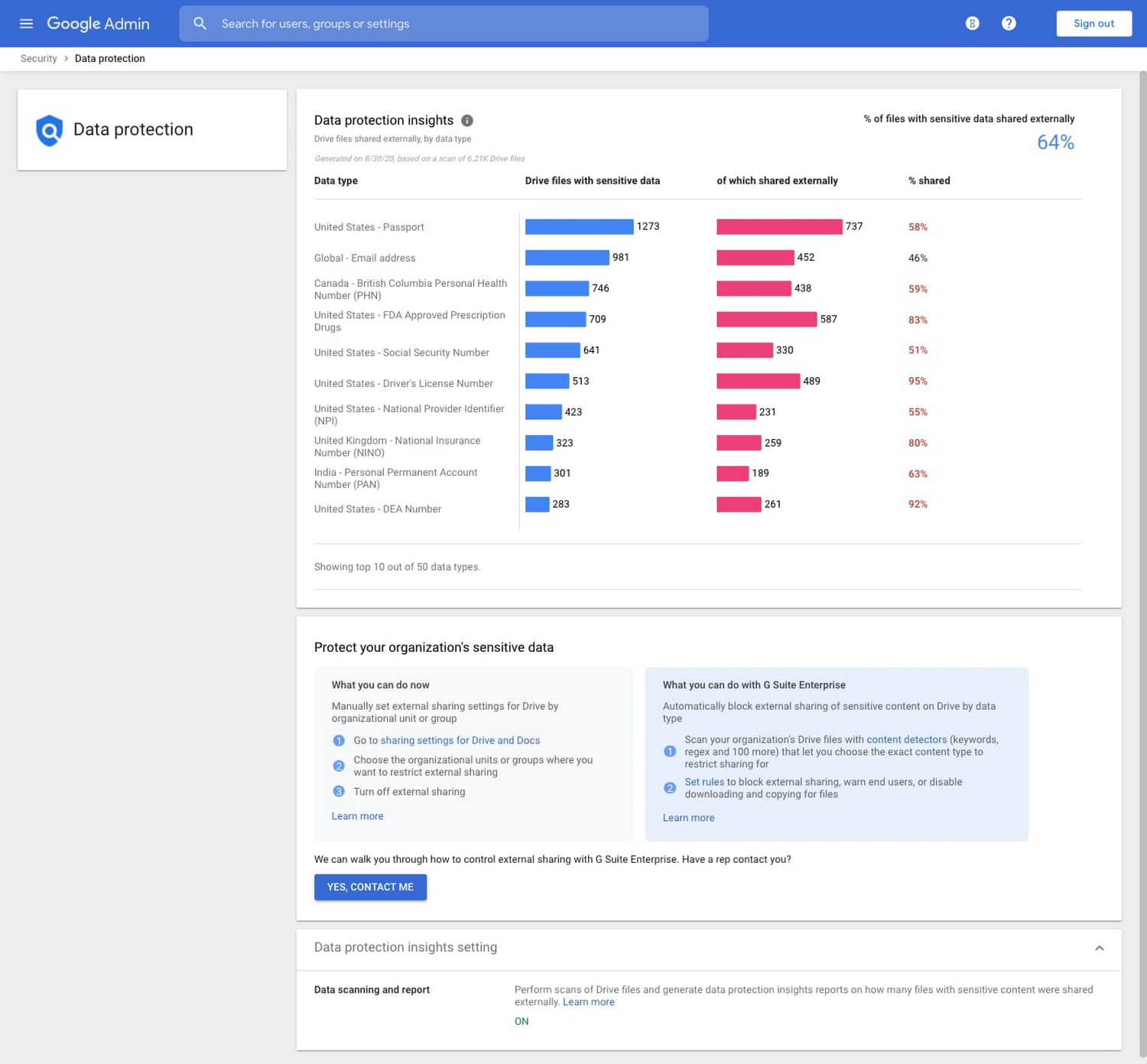
Next, we’re helping you take visibility to the next level with actionable insights that help you keep your organization’s data safe. We’re happy to announce that we are rolling out the general availability of data protection insights in the next couple weeks to help you identify the top sensitive data types for your organization. Beyond just being able to see what sensitive data your organization is dealing with, we’re helping you prioritize and focus your data protection efforts. Data protection insights will be available to G Suite Business customers, in addition to the G Suite Enterprise customers.
With these tools, we are giving organizations the ability to manage security-at-scale more effectively and securely, while saving time and effort. To help you navigate the latest thinking in cloud security, explore the latest installment of our Google Cloud Security Talks, on-demand now.



Comments
Post a Comment